



This blog post describes how to configure the Mikrotik router to act as a PPPoE server with IPv6 enabled.
Check out:
Starting from RouterOS 6.48.2 DHCPv6, Prefix Delegation with Radius server over PPPoE tunnel works correctly (don’t opt for the earlier versions of RouterOS).
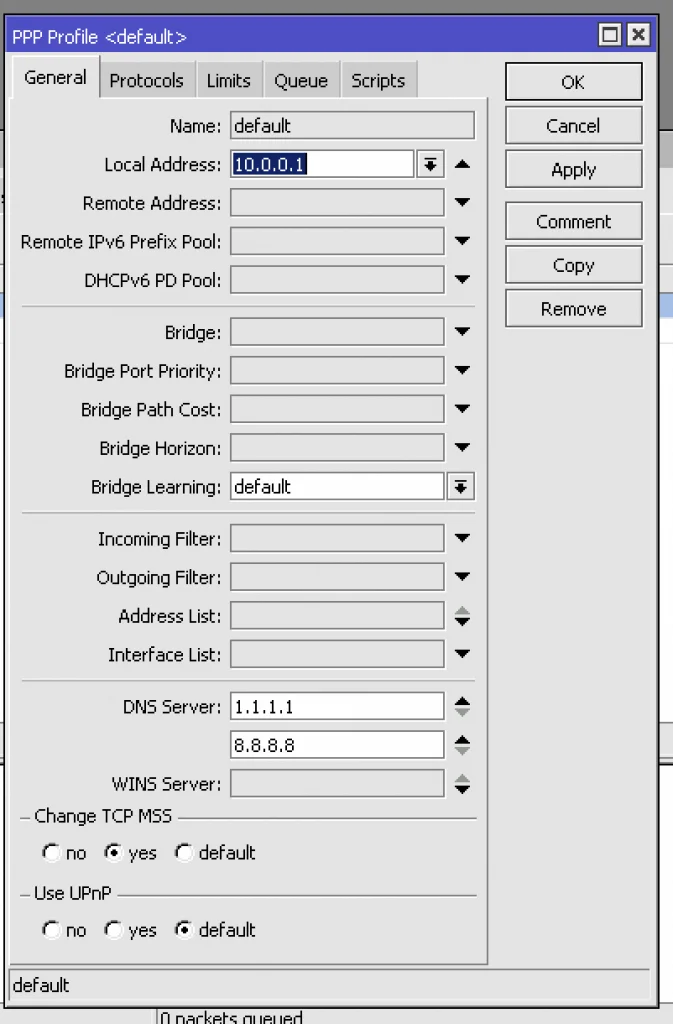
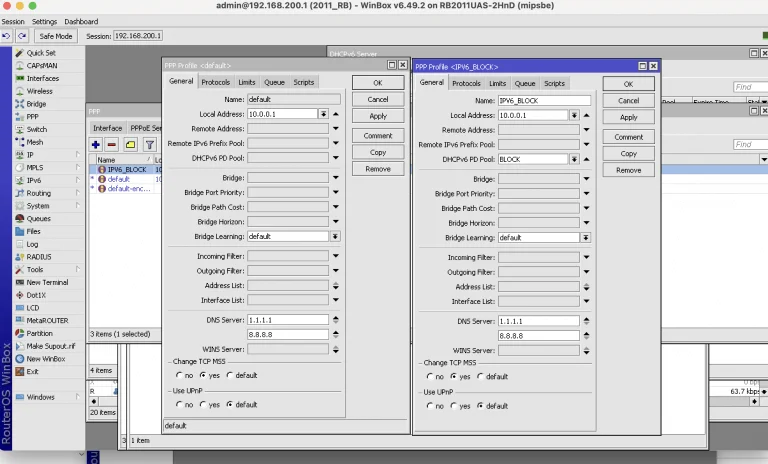
First, you have to create the Mikrotik PPPoE server with Radius authentication. Take a look at the screenshot where the basic PPPoE server settings of RouterOS are depicted. Don’t mind other configurations to make IPv6 work.
Note that you don’t have to specify IPv6 pools since they’re assigned by the Radius server.
Unfortunately, there is no way to assign public IPv6 to the WAN PPPoE interface of the customer via the Radius server. PPPoE works well on the local link addresses even without this feature.
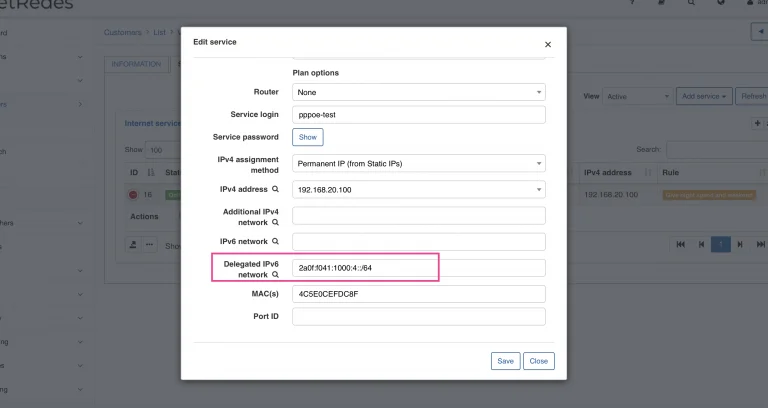
Speaking of Splynx configuration, you should configure the customer internet service with “Delegated IPv6 network”.
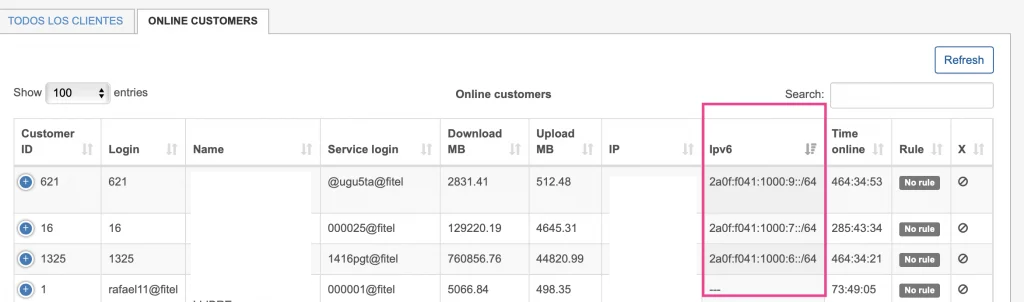
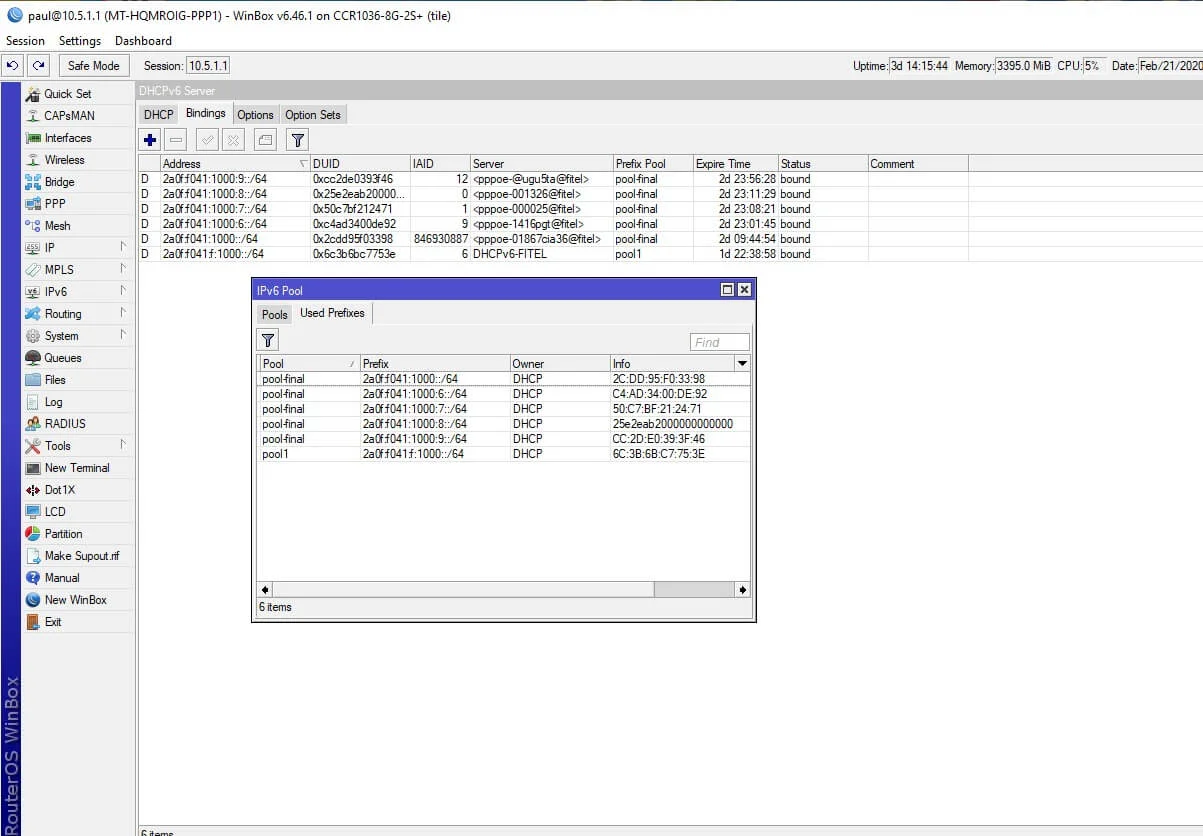
When the PPPoE session is connected and IPv6 assigned, you can find it in the “DHCPv6 Active Leases”. Here’s an example:
Usually, IPv4 traffic gets blocked when the customer’s IP address is added to the address list and traffic is redirected. Another way is to assign the IP address from a special pool for the blocked subscribers to a customer. You cannot complete this configuration with IPv6 because currently, Radius cannot set the special pool or engage with the IPv6 of the end-user.
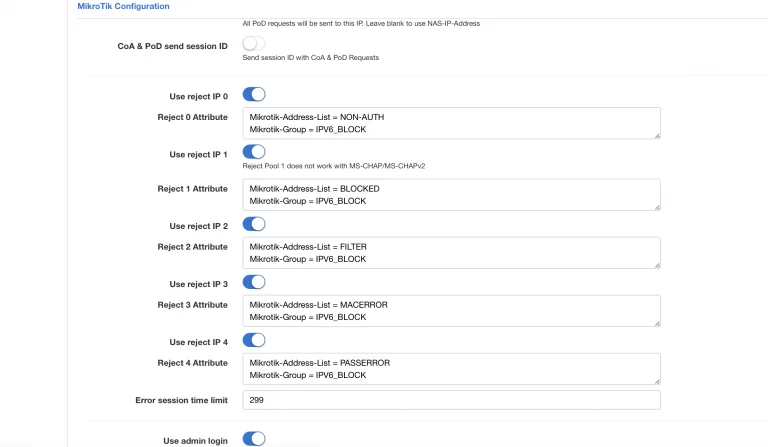
The only possible way is to have several profiles configured in the Mikrotik PPPoE server. Radius’s profile can be sent to the Mikrotik PPPoE router via the Mikrotik-Group attribute. Here is a description of the attribute from the Mikrotik website:
In this case, you need to set two profiles: the default and the block ones. The block profile should have an IPv6 pool for blocking.
The default profile is used for authenticated users, and the block one is assigned to the locked or non-authenticated customers.
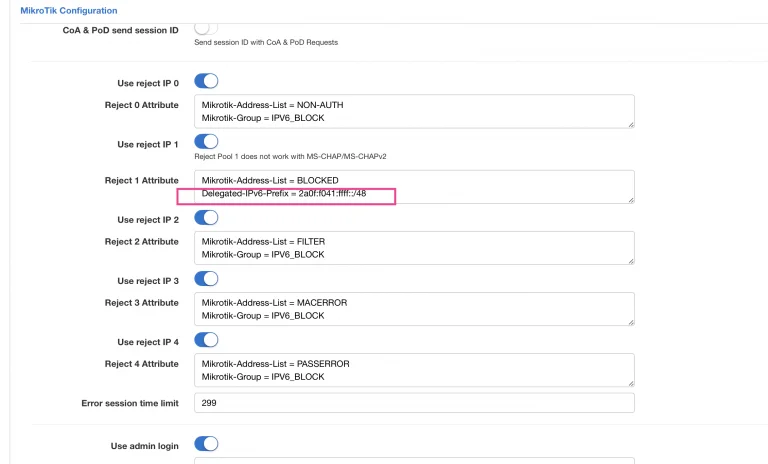
The second way and the easier one is to define statically a pool inside Splynx blocking Radius configuration. This will work both for PPPoE and native DHCPv6 authentication.
For example, Delegated-IPv6-Pool = 2a0f:f041:ffff::/48. Take a look at the screenshot below.
The second option and easier one is to define statically a pool inside Splynx blocking Radius configuration. This will work both for PPPoE and native DHCPv6 authentication. For example Delegated-IPv6-Pool = 2a0f:f041:ffff::/48, please check the screenshot below.
Mikrotik can act as a home router or CPE with IPv6 support enabled. First of all, you need to activate the IPv6 package that is always disabled by default.
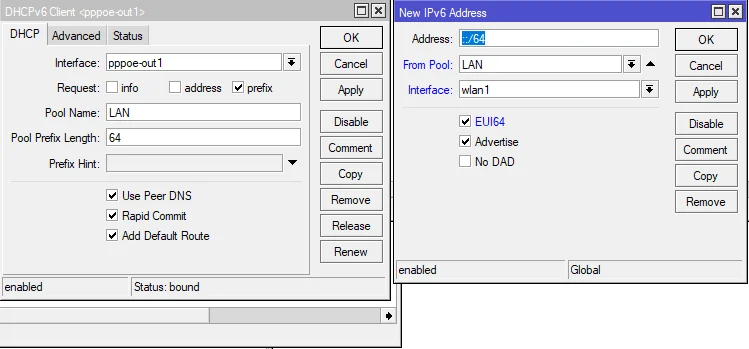
For instance, you have a WAN interface with PPPoE-client and Bridge configured for LAN interfaces. After the activation of the PPPoE interface and setting user/password there, you should enable the DHCPv6 client on the PPPoE-client interface. DHCPv6 client should receive the delegated prefix from the PPPoE router (yes, it sounds weird, but there is a DHCP client running over the PPPOE client for IPv6 because originally there was no way to provide a delegated prefix to the home router).
Remember to configure the pool name and create an IP address assignment with SLAAC on the LAN interface. It’ll be easier simply to copy the configuration captured on the screenshot below ↓
Find out how Splynx helps ISPs grow
Learn more